

Perfect, thanks a million! I’ll be getting on them soon!
InfoSec Person | Alt-Account#2


Perfect, thanks a million! I’ll be getting on them soon!


Could you link the page which shows your exact config at that price? I can’t find anything like that. KVM, AMD, Windows VPS - I looked at all three but none suggest the price you’ve written.
That price sounds like a steal, and I’d love to get it if possible. I currently pay $6/month per VPS with Digital Ocean


Are you talking about this: I have toyota corola?


I think the difference lies in two things:
You can share an article from a user of a different instance. In this case, your instance will have to look up the rel=“author” tag and check whether the URL is a fediverse instance. I’m not sure whether this is scalable as compared to a tag that directly indicates that the author is on the fediverse. Imagining a scenario where there are 100, 1000, 10,000, or 100,000 instances on different versions.
The tag is to promote that the author is on the fediverse. If the rel=“author” tag points to twitter for example, maybe Eugen Rochko + team didn’t want a post on the fediverse to link to twitter.
These are my thoughts and idk if they’re valid. But I think just reusing the rel=“author” isn’t the most elegant solution.
I know that mastodon already uses rel=“me” for link verification (I use it on mu website + my mastodon account), but that’s a different purpose - that’s more for verification. There’s still no way of guaranteeing that the rel=“author” tag points to a fediverse account. You’re putting the onus on the mastodon instance.


It works in a pretty neat way:
We’ve decided to create a new kind of OpenGraph tag—the same kind of tags you have on your website to determine which thumbnail image will appear on the preview for the page when shared on Discord, iMessage, or Mastodon. It looks like this: <meta name=“fediverse:creator” content=“@Gargron@mastodon.social” />.
via: https://blog.joinmastodon.org/2024/07/highlighting-journalism-on-mastodon/
The debug version you compile doesn’t affect the code; it just stores more information about symbols. The whole shtick about the debugger replacing instructions with INT3 still happens.
You can validate that the code isn’t affected yourself by running objdump on two binaries, one compiled with debug symbols and one without. Otherwise if you’re lazy (like me 😄):
https://stackoverflow.com/a/8676610
And for completeness: https://gcc.gnu.org/onlinedocs/gcc-14.1.0/gcc/Debugging-Options.html
Excellent question!
Before replacing the instruction with INT 3, the debugger keeps a note of what instruction was at that point in the code. When the CPU encounters INT 3, it hands control to the debugger.
When the debugging operations are done, the debugger replaces the INT 3 with the original instruction and makes the instruction pointer go back one step, thereby ensuring that the original instruction is executed.
https://en.wikipedia.org/wiki/INT_(x86_instruction) (scroll down to INT3)
https://stackoverflow.com/a/61946177
The TL;DR is that it’s used by debuggers to set a breakpoint in code.
For example, if you’re familiar with gdb, one of the simplest ways to make code stop executing at a particular point in the code is to add a breakpoint there.
Gdb replaces the instruction at the breakpoint with 0xCC, which happens to be the opcode for INT 3 — generate interrupt 3. When the CPU encounters the instruction, it generates interrupt 3, following which the kernel’s interrupt handler sends a signal (SIGTRAP) to the debugger. Thus, the debugger will know it’s meant to start a debugging loop there.
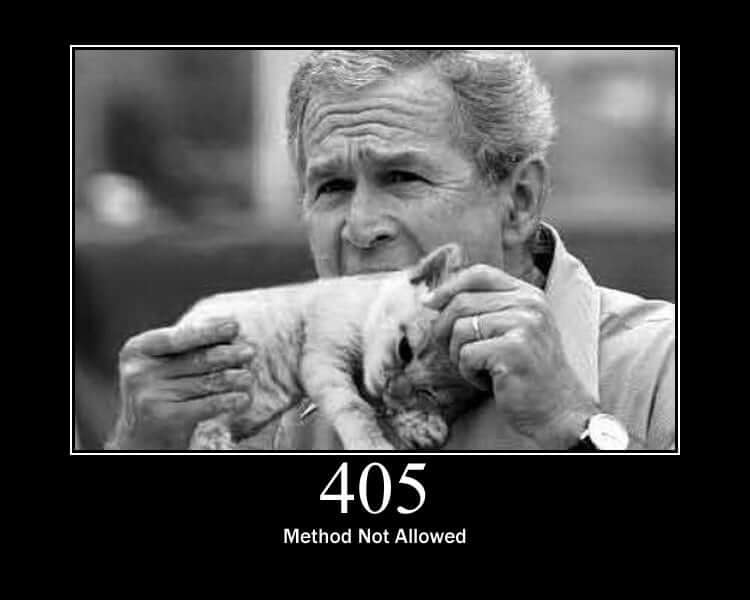
Surprised no one’s mentioned HTTP Cats yet:
Personally, HTTP 405 (Method not allowed) is my favorite:
That’s crazy helpful - thanks!